by Ian Hindley
Overview
Versa Application Identification Library (AIL) is a database containing signatures to detect and identify more than 4800 pre-defined applications such as YouTube and Microsoft Teams. The database is a component of VOS (Versa Operating System) and used for SSE and SDWAN use-cases.
Applications contained within the AIL can be referenced by Network Administrators as match criteria for policies such as Firewall; QOS and SDWAN Traffic Steering.
Updates to the AIL are provided in Security Pack (SPack) updates. These allow the AIL database to recognize additional applications or changes to existing applications.
SPack updates can be automatically scheduled for download and install on SDWAN and SSE Gateway devices. This ensures updates to application signatures are automated and require no human intervention.
In some cases, an upgrade of the AIL ProtoBundle is required to take advantage of new applications provided in SPack updates. Hence it is recommended AIL ProtoBundle versioning is monitored and managed to ensure optimal application recognition by VOS devices.
Although out of scope for this document, the AIL ProtoBundle upgrade process is described here – https://docs.versa-networks.com/Management_and_Orchestration/Versa_Director/ Configuration/Use_Security_Packages_(SPacks)#Upgrade_the_Application_Engine_Protocol_Bundle
Policies and ‘Match’ Criteria
For SSE and SDWAN use-cases, policies are created by the Corporate Network Administrator for a variety of purposes. Firewall; QOS; SDWAN Traffic Steering; SSE Secure Client Access are all examples of policies that can be configured to control traffic transiting the network.
In all cases, policies use a combination of match criteria (to uniquely identify traffic) and policy action (for example, permit or deny) to associate flows of data with a specific outcome. For example:
- In a firewall context, traffic destined to a specific IP address (policy match criteria) could be permitted (policy action), whereas traffic destined to another IP address (policy match criteria) could be denied (policy action)
- In a QOS context, traffic marked ‘EF’ (policy match criteria) is policed to 5Mbps (policy action) to ensure it doesn’t starve other forwarding classes when transmitting data onto the local WAN interface
- In an SDWAN Traffic Steering context, traffic destined to a database (policy match criteria) should pass over the lowest latency WAN link (policy action) between Branch and DataCentre
- In an SSE context, end user devices considered ‘compliant’ by the Mobile Device Manager (MDM) such as Microsoft InTune (policy match criteria) are permitted to connect to the SSE Gateway (policy action)
There are multiple options to identify traffic via match criteria. Examples include:
- Source – IP address; Port; Zone; Geo-Location
- Destination – IP address; Port; Zone; Geo-Location
- Protocol
- Time of Day
- DSCP
- User or User Group
- End device compliance
Such match criteria can be used in isolation or in combination with one another to uniquely identify traffic and associate it with a policy action.
Another match criteria available to the Network Administrator is ‘application’. Selecting an application allows the Network Administrator to match on an application signature. Such examples include YouTube as shown in the example screenshot below:

The advantage of referencing an application is, changes in identifying traffic is no longer a manual process. Instead, VOS (Versa Operating System) automates application signature updates. This avoids the Network Administrator monitoring IP address; port; protocol characteristics which is both time consuming and prone to error. Therefore, as the attributes identifying the application dynamically change, so too does the application signature hosted on the VOS appliance. At the same time, this is achieved without Network Administrator intervention.
Versa AIL and SPack Updates
The Application Identification Library (AIL) is a database containing signatures to detect and identify applications. The AIL is a component of VOS software and is preinstalled on each Versa SSE Gateway or SDWAN CPE device.
Updates to the AIL are delivered through Security Pack (SPack) updates. When VOS devices are configured to automatically download and install SPack updates, any changes to the application ‘signature’ contained within the AIL are automatically amended. This ensures policy referencing an application is using the latest signatures with which to evaluate transiting traffic.
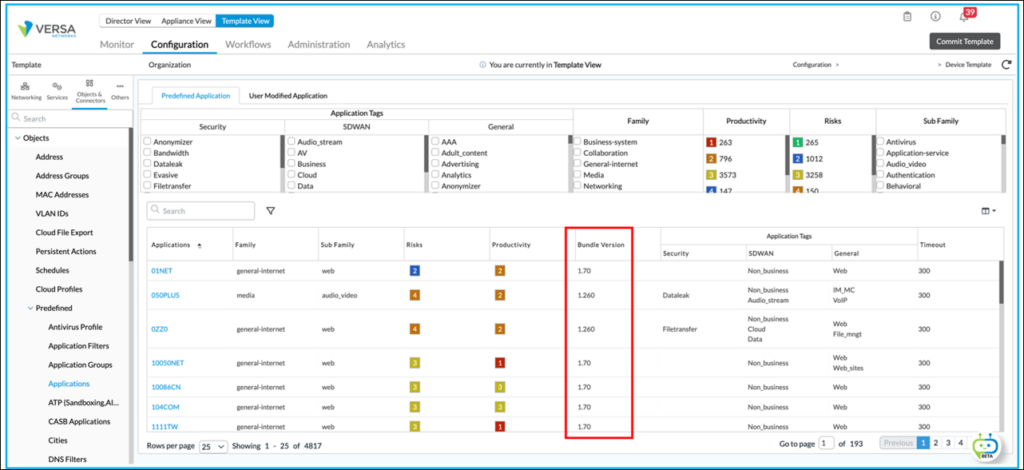
In the case of new application signatures, the VOS device may require an update to the AIL Protocol Bundle (ProtoBundle) to recognise the new application. This can be determined using Versa Director. By navigating to the VOS devices’ Objects & Connectors > Objects > Predefined > Applications, all the applications in the AIL are listed. In addition, the corresponding AIL ProtoBundle version required for that application is also listed. This is shown in the screenshot below:
The required application signature Bundle Version can be compared with the VOS installed version by navigating to:
- In Director view:
- Select the Configuration tab in the top menu bar
- Select Devices > Devices in the horizontal menu bar
- Select a device name in the main panel
- Select Administration in the top menu bar
- Select Organization > Security Package in the left menu bar
- As shown in the screenshot below, the installed Protocol Bundle of the selected VOS device is displayed:
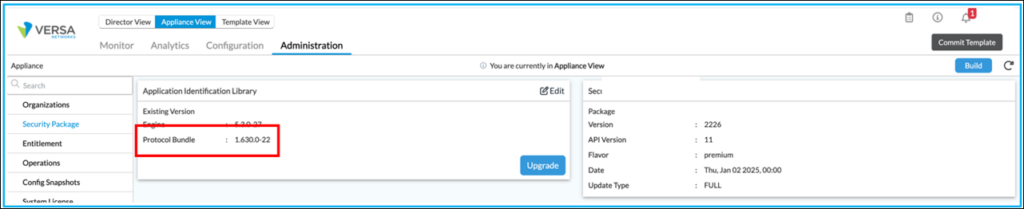
In this example, any applications in the AIL requiring Bundle Version v1.630.0-22 or older are supported by this VOS device.
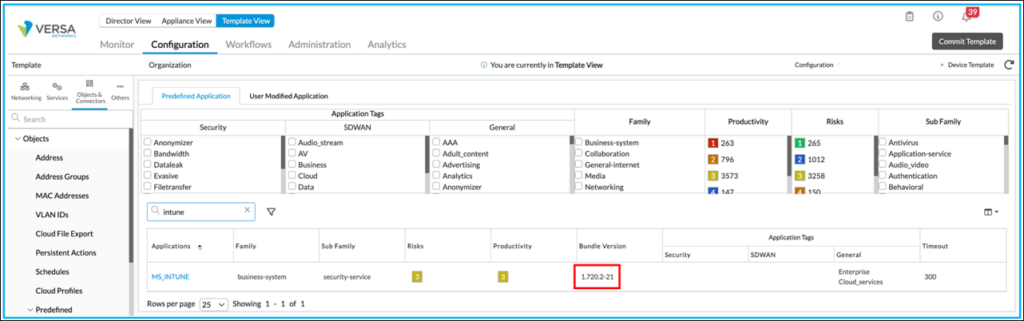
Using Microsoft InTune as an example, an application signature exists for policy selection. In the following screenshot, this is shown from Concerto although the same is available from the Versa Director UI.

Using Versa Director, it states ‘Bundle Version’ v1.720.2-21 is required for the VOS device to recognize the application:
However, the VOS device is running Protocol Bundle v1.630.0-22:

Consequentially, the application isn’t recognised by the VOS device. This will prevent matches in policy:

To recognise the application signature, an upgrade of the AIL ProtoBundle on the VOS device is required. Unlike SPack updates, AIL ProtoBundle updates are not installed automatically. These are manually performed. Additionally, the upgrade affects the operation of the VOS device as VOS services are automatically restarted post the upgrade.
In this example, the ProtoBundle on the VOS device was upgraded as shown in the screenshot below:
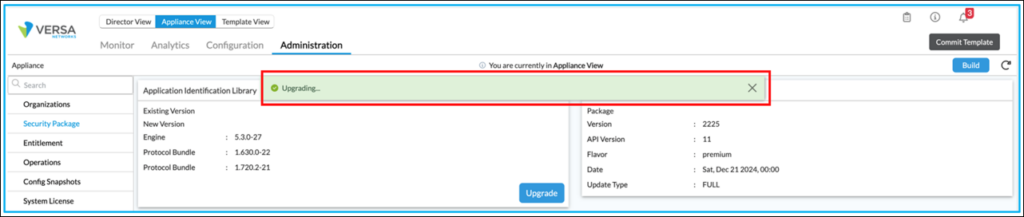
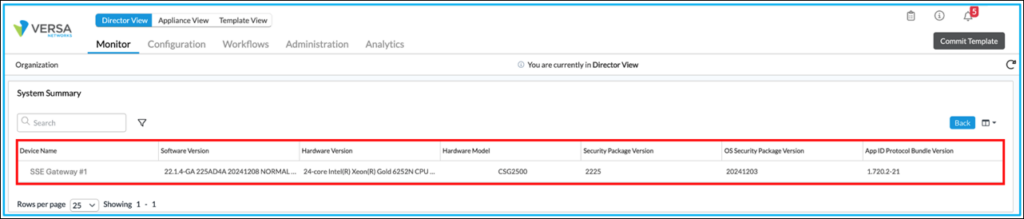
Once complete, the reported ProtoBundle was the same version as required by the application signature (i.e. v1.720.2-21):
As shown in the screenshot below, the same VOS device is now able to recognise MS_INTUNE packets due to the AIL ProtoBundle upgrade. This ensures matches in policy occur and the correct policy action can be enforced:

In this example involving Microsoft InTune, an upgrade of the AIL ProtoBundle is required to take advantage of new applications provided in SPack updates. Hence it is recommended AIL ProtoBundle versioning is monitored and managed to ensure optimal application recognition by VOS devices.
AIL ProtoBundle Auditing
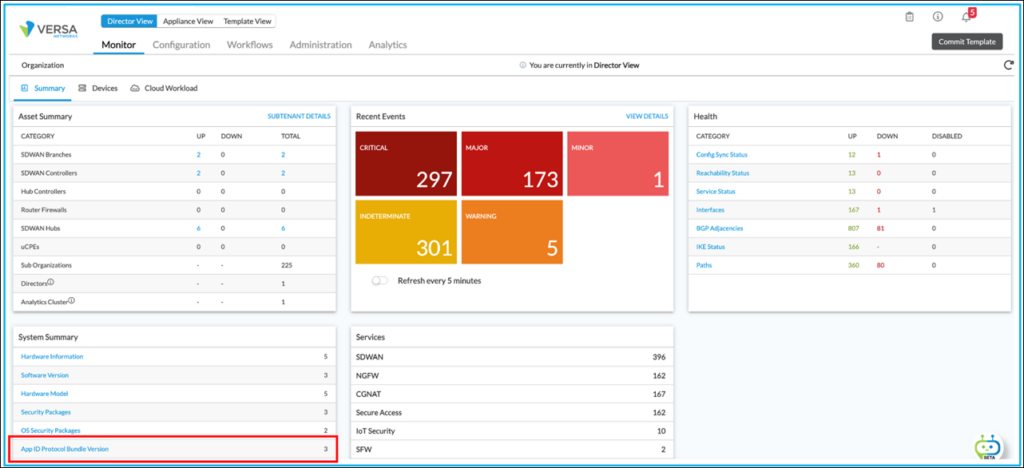
A network wide audit of AIL ProtoBundle versioning can be performed through Versa Director. This simplifies which VOS devices are running which ProtoBundle versions and helps identify those devices that may require upgrading.
To perform the audit, in Versa Director, navigate to Monitor > Summary. Ensure ‘Organization’ is set to the parent org name. The number of versions found across the network is displayed in the ‘System Summary’ section as shown below. In this example, there are three different AIL ProtoBundles installed across the estate:
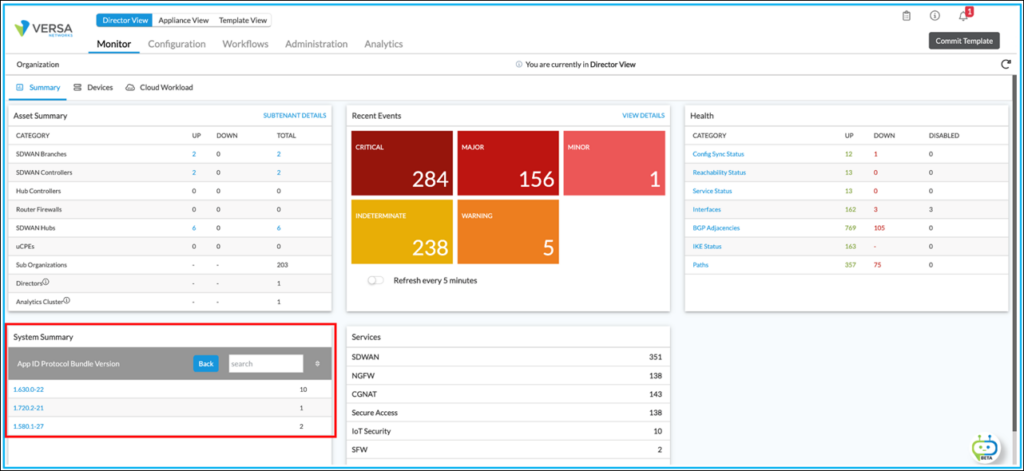
By selecting the hyperlink, ProtoBundle versions can be displayed. In this case, they are v1.580.1-27; v1.630.0-22 and v1.720.2-21. The output also displays the number of VOS devices running each ProtoBundle version:
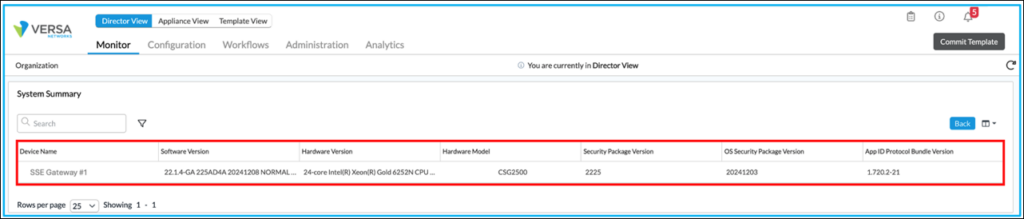
By selecting each version (by clicking on its hyperlink), a list of devices running that version of the AIL ProtoBundle are displayed. In this example, all VOS devices running AIL ProtoBundle v1.720.2-21 are listed:
More information regarding SPack and AIL and how these are upgraded can be found here – https://docs.versa-networks.com/Management_and_Orchestration/Versa_Director/Configuration/Use_Security_Packages_(SPacks)#Upgrade_the_Application_Engine_Protocol_Bundle
Conclusion
The Versa Application Identification Library (AIL) is a critical component for enabling precise application detection and policy enforcement within VOS-powered environments. By leveraging regular Security Pack (SPack) updates and monitoring AIL ProtoBundle versions, organizations can ensure their SDWAN and SSE solutions remain current with the latest application signatures. This proactive approach maximizes the effectiveness of security, quality of service, and traffic management policies, while minimizing manual intervention and operational overhead. Consistent management of AIL and its updates is essential for maintaining optimal application recognition and network performance.





