SSL Inspection
by Rengaramalingam A
SSL / TLS Inspection is the process where the SSL / TLS encrypted traffic is intercepted between a client and server machine. This interception can be initiated by either the client towards the server or vice-versa.
Although all traffic send over SSL / TLS is encrypted, there could also be instance where malicious content also gets encrypted and pass on as legitimate traffic thus getting past the security perimeter of the Branch.
“Research indicates that encrypted connections have become the preferred method for malware delivery, putting organizations that don’t decrypt traffic at higher risk”
WatchGuard, Mar 2023
Versa Secure SD-WAN SSL Inspection is a feature by which the Versa Operating System inspects the SSL certificates for expired or rogue certificates there by protecting the end hosts connected on the LAN.
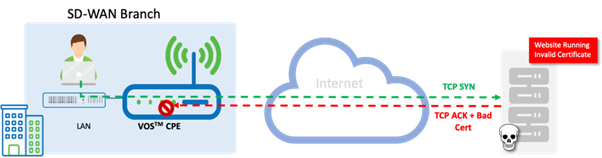
High Level Topology
Here we have a user behind a Versa SD-WAN appliance connected to the Internet and trying to access a web portal that is having invalid/rogue SSL Certificates. The VOS, by inspecting the Server Response and looking deep into the SSL Certificates, detects the anomalies, and instead of forwarding the server response to the end host, the VOS drop/rejects the bad SSL packets and in turn protects the end host.
Configuration
Objectives
A. Generate a Key and Self-Signed Certificate on the Versa appliance. (Customers can choose to use registered certificate in real world)
B. Create a Decryption Profile and associate this into a Decryption Policy to inspect the Traffic.
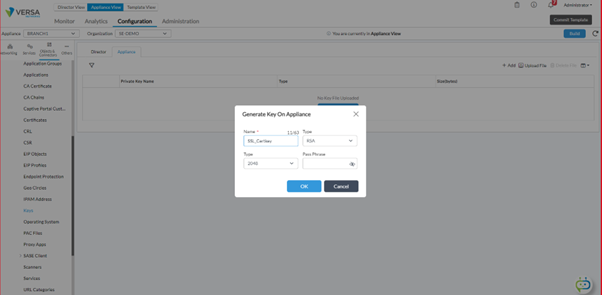
Step 1: Generate a Key in the Appliance Context.
Step 2: Generate a Self Signed Certificate on the Appliance.
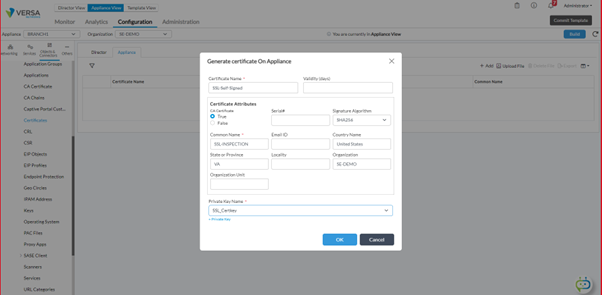
CA certificate ideally is not required for SSL inspection. However, since we are using same profile for inspection and decryption, it is required to create a certificate and attach it.
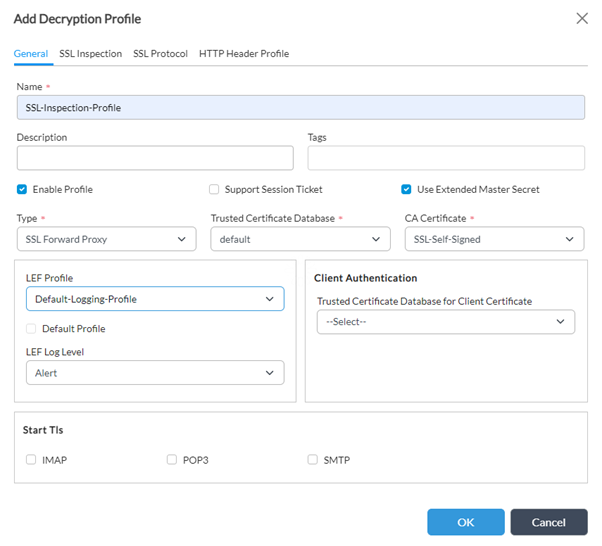
Step 3: Configure an SSL Inspection Profile and map the Self Signed Certificated created above under the CA Certificate in the Profile Choose the Decryption type as 'SSL Forward Proxy' and choose 'reject' for all SSL Certificate Checks.
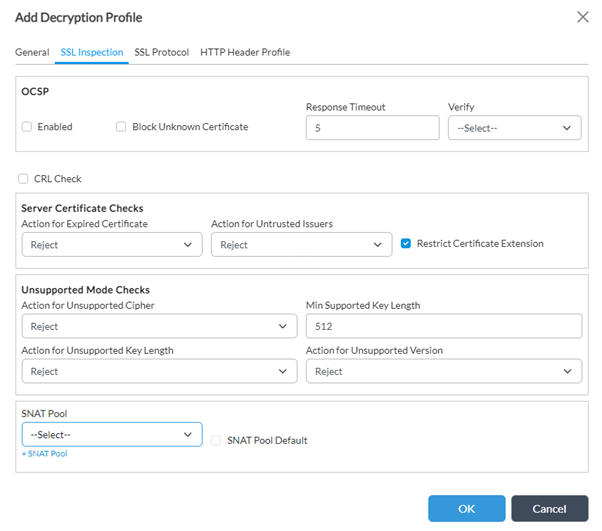
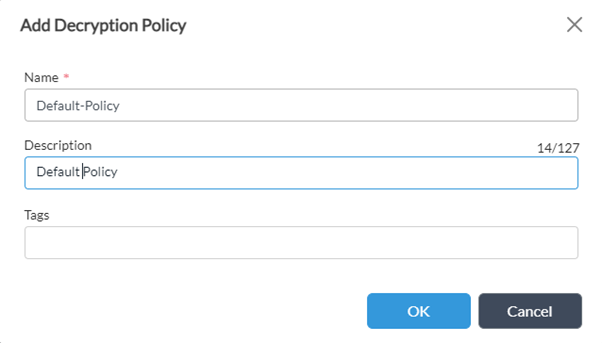
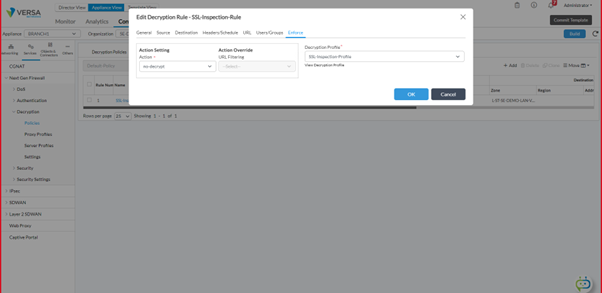
Step 4: Create a Decryption Policy - 'Default Policy' and Create a Rule to match all Traffic going towards Internet. In the Enforce Tab, choose Action as 'no-decrypt' and map the Decryption Profile created earlier.
Verification
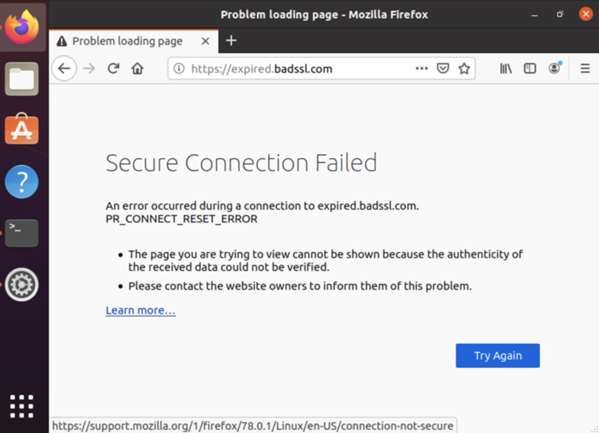
Initiate traffic by visiting the site https://badssl.com
From within the site choose any of the links with the ‘bad ssl’ category defined in it.The site gets blocked and does not open.
On receiving a bad SSL response from the site, the VOS automatically blocks the traffic.
Logs on CLI and Analytics
From within the CLI, we can observe the hit count on the SSL-Inspection-Rule policy.
b[ok][2023-05-22 08:09:32]
admin@BRANCH1-cli> show orgs org-services SE-DEMO security decryption-policies rules decrypt-policy-stats
HIT
NAME NAME COUNT
--------------------------------------------
Default-Policy SSL-Inspection-Rule 36
[ok][2023-05-22 08:11:27]
admin@BRANCH1-cli>
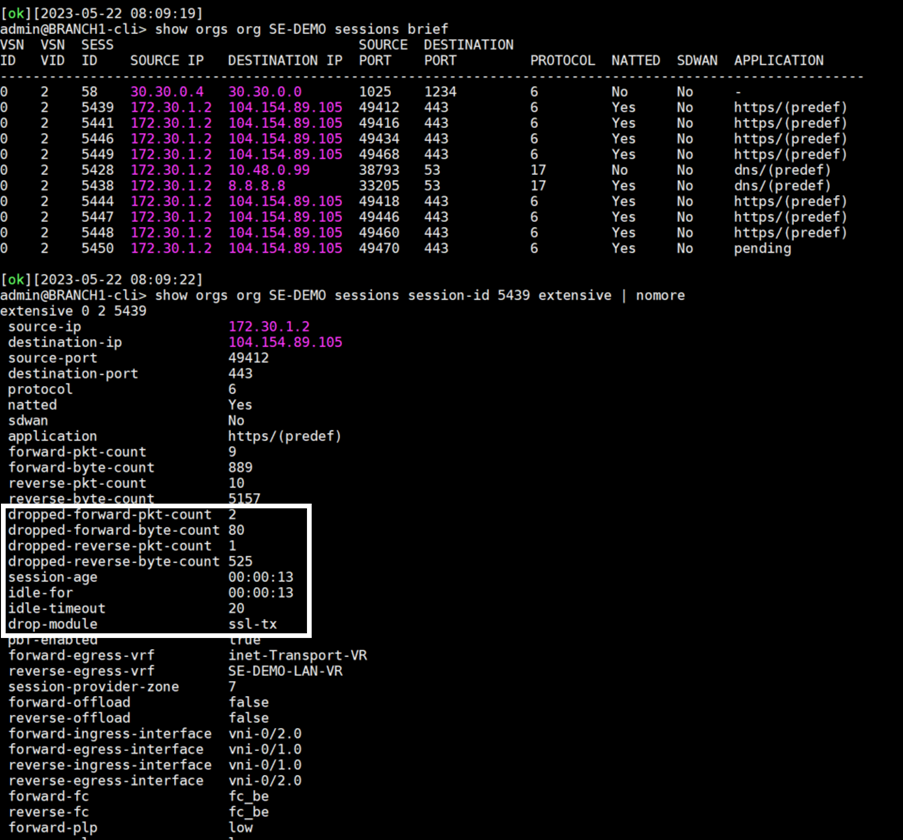
On the analytics, the SSL decryption tab shows the SSL Decryption logs. The Action Taken defines if the site TCP sessions have been allowed or rejected and the reason for rejection.
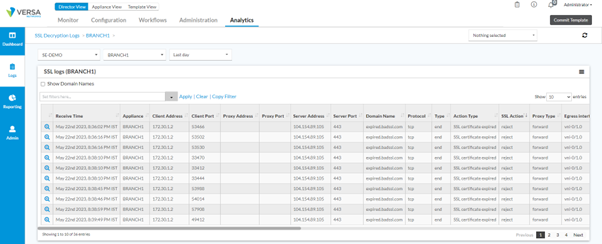
| Receive Time | Log |
| May 22nd 2023, 8:36:02 PM IST | 2023-05-22T15:06:02Z sslSessionLog, tenant=SE-DEMO, applianceName=BRANCH1, srcPort=53466, destPort=443, ingIf=vni-0/2.0, egrIf=vni-0/1.0, toCountry=United States, protocolId=6, fromZone=Intf-tenant-lan-Zone, fromUser=Unknown, toZone=RTI-inet-Zone, srcAddr=172.30.1.2, destAddr=104.154.89.105, toLatLon=38.0,-97.0, toGeoHash=9yg00t, obsTime=2023-05-22T15:06:22Z, txBytes=889, txPkts=9, rxBytes=5157, rxPkts=10, serverAddr=104.154.89.105, serverPort=443, domainName=expired.badssl.com, certIsSelfSigned=0, publicKeyLen=2048, eventType=end, actionType=SSL certificate expired, sslAction=reject, decryptProfileName=SSL-Inspection-Profile, policyRuleName=SSL-Inspection-Rule, policyAction=no-decrypt, proxyType=forward, flowKey=0x646b84d9010002001454, clientAddr=172.30.1.2, clientPort=53466, rcvTimeSec=2, sessLenBkt=0, flowDuration=504Summary |
Summary
This article explained the configuration behind SSL-Inspection and how it can be used to secure the Hosts behind a Versa Secure SD-WAN.





