by Tamilvanan S
Versa’s Zone Protection is one of the features of Versa VOS’s Stateful Firewall which helps to prevent a Network attack on an Appliance targeted at compromising the network performance or resource consumption. Versa VOS by default operates in stateful mode and creates a session for every flow going through it.
Zone Protection prevents resource consumption due to flood, scan, or network attacks before the Versa SD-WAN appliance creates a session.
Zone Protection is used to detect and take immediate action against rogue or malicious packets.
High-Level Topology
We have a Versa VOS appliance connected to the Internet and a Web Server on the LAN.
Zone Protection Configuration
Enable the Zone protection profile configuration on the respective template or on the device.
Select Networking —> zone protection profile —> Add
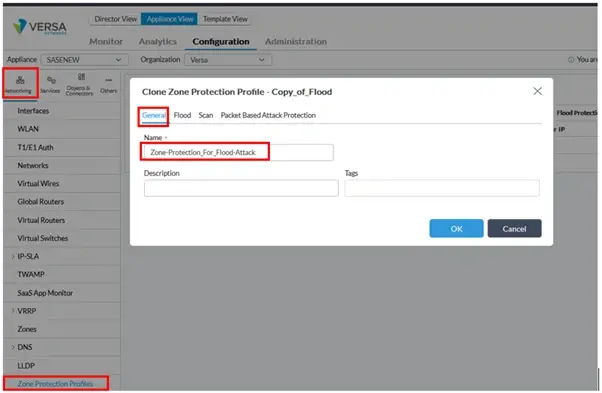
Enable the respective protocol that needs to be mitigated by flood attacks. Set the values as per the requirement or bandwidth calculation.
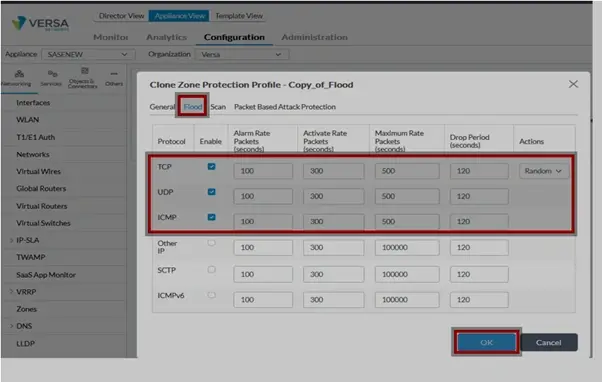
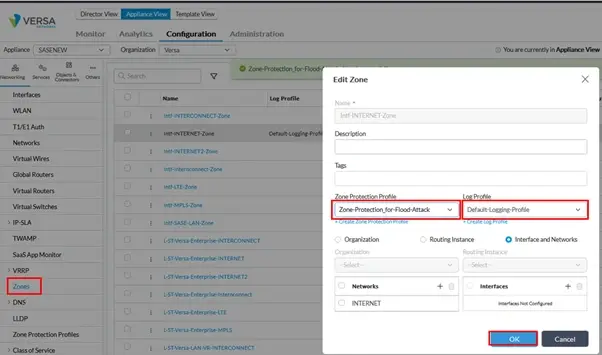
Apply the Zone Protection profile to the Internet/External interface or the interface that needs to be mitigated from flood attacks.
Select the Zone protection profile from the drop-down and select the Log Default Log profile.
Verification post executing an attack
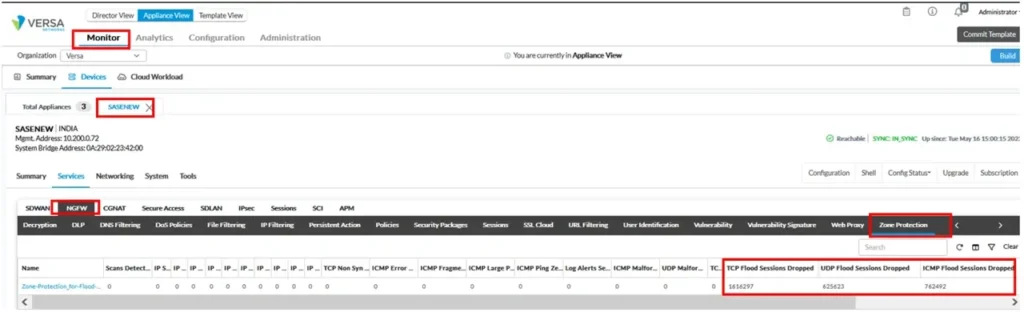
Select respective Appliance → Monitor → Services → NGFW → Zone protection
Counters against “TCP/UDP/ICMP Flood Sessions dropped” are incremented substantially, indicating that Versa FlexVNF Zone Protection Module is in action and preventing a resource consumption attack.
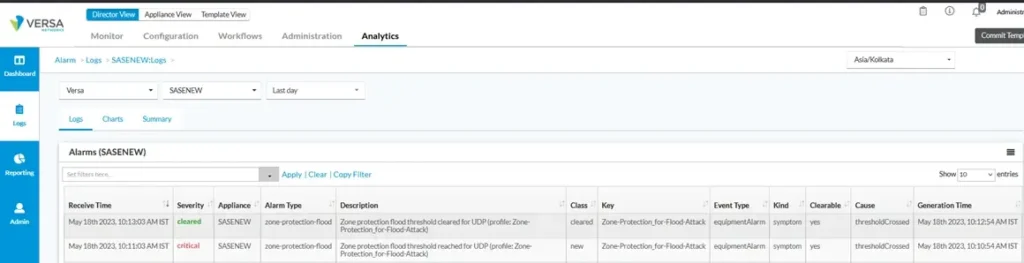
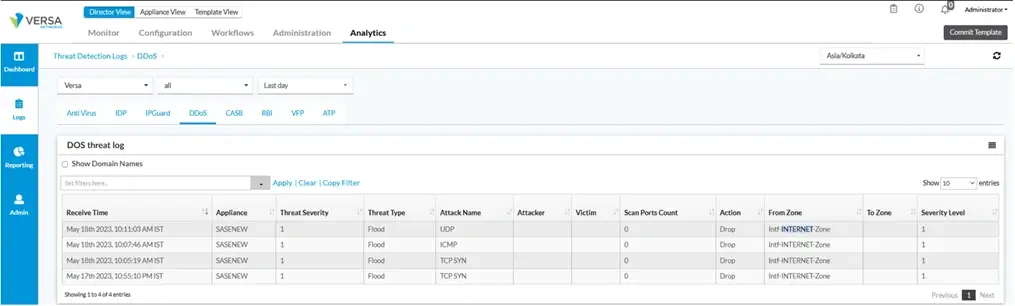
Analytics logs
Analytics Action types against Flood attacks will vary from Allow to Random Early Drop(RED) to Drop depending on at what rate Flood attack is being identified & varying. Please know as Zone Protection Profile does not have a Classifying ability, analytics logs won’t specify the Attacker’s IP Address. In order to find out an Attacker’s IP Address, please use DoS Protection Classified Profile as presented in this wiki article: DOS Protection: Classified Profile