Is Your ZTNA Solution Really Zero Trust?
 By Avic Bose
By Avic Bose
Principal Systems Engineer, Versa Networks
December 5, 2022
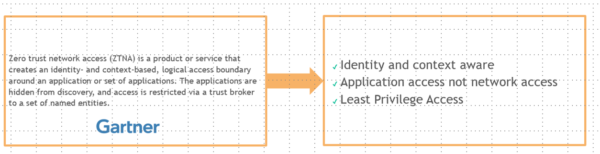
Zero Trust Network Access (ZTNA), also referred to as Software Defined Perimeter (SDP), was coined by Gartner in 2019 to describe products and services which enables secure connections to private applications centered on Zero Trust Model. Gartner defines Zero Trust Network Access as “a product or service that creates an identity and context-based, logical access boundary around an application or set of applications. The applications are hidden from discovery, and access is restricted via a trust broker to a set of named entities.”
Need for ZTNA
With the dissolution of the traditional security perimeter, increased proliferation of SaaS applications, increased migration of workloads to public cloud, dramatic increase in remote work force made necessary due to COVID-19 coupled with increased adoption of BYOD policies in most enterprises have altered the threat landscape dramatically. This has triggered the need for implementing a zero-trust security framework to enable enterprises to provide secure access to private applications and SaaS applications using a zero-trust model.As per the initial SASE framework, which was published by Gartner in 2019, Zero Trust Network Access is one of the Core components of the Secure Access Services Edge and hence almost all the SASE Vendors specifically Secure Services Edge Vendors offer, ZTNA as a service as a part of their overall SSE solution from their cloud hosted gateways.
What is Zero Trust?
Zero trust was first conceptualized by Forrester Analyst John Kindervarg in the year 2010. Zero Trust as defined by Gartner is a simplified way of describing an approach where implicit trust is removed from all computing Infrastructure. Zero trust is a way of thinking, not a specific technology or architecture. It’s about zero implicit trust, as that’s what customers want to get rid of.” In more simple terms, Zero Trust can be defined as “Never Trust Always Verify“. Zero Trust is based on 3 fundamental principles as illustrated in the diagram below: Verify Explicitly – Verification should be done to verify the identity of the user, the context of the user and most importantly the data/traffic that is being exchanged.
Verify Explicitly – Verification should be done to verify the identity of the user, the context of the user and most importantly the data/traffic that is being exchanged.
 Use Least Privilege Access – The principle of least privilege is an information security concept which maintains that a user or entity should only have access to the specific data, resources and applications needed to complete a required task.
Use Least Privilege Access – The principle of least privilege is an information security concept which maintains that a user or entity should only have access to the specific data, resources and applications needed to complete a required task.
 Assume Breach – This entails that organizations should assume eventually that the cybersecurity defenses would be compromised, and attackers will gain either complete or partial access to their networks. Therefore, organizations should continuously keep on proactively monitoring for threats in their environment.
Assume Breach – This entails that organizations should assume eventually that the cybersecurity defenses would be compromised, and attackers will gain either complete or partial access to their networks. Therefore, organizations should continuously keep on proactively monitoring for threats in their environment.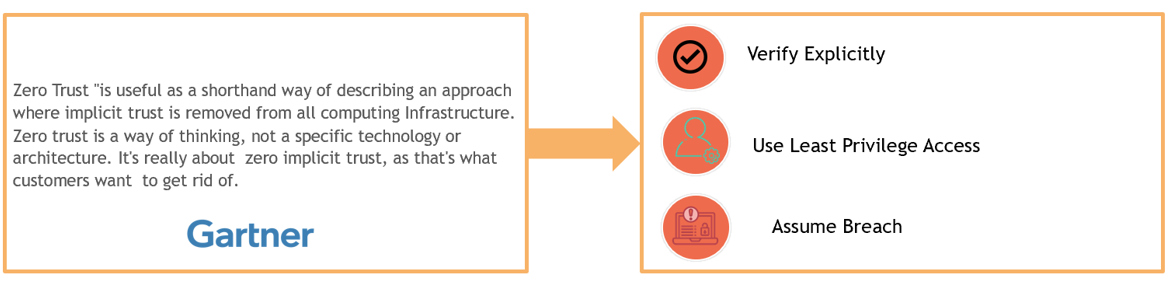
Are Present ZTNA Solutions really Zero Trust?
Most of the present ZTNA solutions available today to adhere to the principles of Zero Trust at a minimum, try to implement the following verification capabilities in their product: UserID Verification – The identity of the user for each individual application request is verified by integrating with a User Database (OnPrem or Cloud).
UserID Verification – The identity of the user for each individual application request is verified by integrating with a User Database (OnPrem or Cloud).
 Context Verification – Contextual information is also collected such as Device Posture, Source/Destination Geolocation, IP reputation etc. as a part of the initial verification process and is factored in while making the final decision as to whether to allow the user to have access to the application or not.
Context Verification – Contextual information is also collected such as Device Posture, Source/Destination Geolocation, IP reputation etc. as a part of the initial verification process and is factored in while making the final decision as to whether to allow the user to have access to the application or not.
 Segmenation – Segmentation involves grouping the applications into logical groups and only allow communication between them that is absolutely necessary. This is primarily done to prevent lateral movement from a comprised workload to the rest of the network.
Segmenation – Segmentation involves grouping the applications into logical groups and only allow communication between them that is absolutely necessary. This is primarily done to prevent lateral movement from a comprised workload to the rest of the network.
 Per-App Tunnel – Unlike traditional VPN Solutions which gives access to entire network segment to the remote end-point, Per-App Tunnels in principle are supposed to limit the access of the remote-end point to one specific application end-point which it is authorized to access.
Per-App Tunnel – Unlike traditional VPN Solutions which gives access to entire network segment to the remote end-point, Per-App Tunnels in principle are supposed to limit the access of the remote-end point to one specific application end-point which it is authorized to access.
However, most of the present ZTNA solutions fail to address the below capabilities:
 Device Verification – The identity of the device for each individual application request is verified by integrating with a Mobile Device Management System (OnPrem or Cloud).
Device Verification – The identity of the device for each individual application request is verified by integrating with a Mobile Device Management System (OnPrem or Cloud).
In cases where the Device Identity cannot be verified, the ZTNA solution relies on only the User Identity to establish the trust. This is a weak security posture, because the ZTNA solution does not offer adequate security protection, in case of compromised user credentials, or when unmanaged or BYOD devices are used to access corporate resources or private applications of the enterprise. A ZTNA solution that incorporates Device Authentication, Device Fingerprinting and Device Posture Checks offers the strongest security posture when providing private access to enterprise applications and resources.
 “Content Inspection“ i.e subjecting all traffic from the remote endpoint destined to the private applications with L7 Security inspection checks irrespective of port/protocol. These include but are not limited to scanning the traffic for any malicious content, checking that any file upload to the private application is free from malware and whether any file uploaded/downloaded to/from the private application doesn’t contain any sensitive information.
“Content Inspection“ i.e subjecting all traffic from the remote endpoint destined to the private applications with L7 Security inspection checks irrespective of port/protocol. These include but are not limited to scanning the traffic for any malicious content, checking that any file upload to the private application is free from malware and whether any file uploaded/downloaded to/from the private application doesn’t contain any sensitive information.
Any ZTNA Solution that doesn’t provide “Full L7 Content inspection” capabilities isn’t really Zero Trust in the true sense since it ends up violating the following 2 core principles of Zero Trust Model.
Verify Explicitly
Assume Breach
Therefore, in conclusion any ZTNA Solution which doesn’t offer Device Authentication or full security inspection capabilities for Private Access Traffic cannot be termed as Zero Trust in the true sense. At best, they can be referred to as “Private Access/Remote Access Solutions with partial Zero Trust Capabilities”. Unfortunately, most of the ZTNA solutions which are offered by the existing SASE/SSE Vendors fall into this category since they offer either very limited Device Posture checks and security inspection or no security inspection capabilities for Private Access traffic.

How to Evaluate whether your ZTNA Solution is really Zero Trust?
As a customer to evaluate whether any ZTNA solution which you may have implemented/shortlisted, all you will need answer to these 4 fundamental questions: Does the proposed ZTNA solution incorporate Device Identity into the Contextual information used to determine private application access?
Does the proposed ZTNA solution incorporate Device Identity into the Contextual information used to determine private application access?
 Does the proposed ZTNA solution treat all traffic the same in regard to security inspection regardless of source or destination?
Does the proposed ZTNA solution treat all traffic the same in regard to security inspection regardless of source or destination?
 Does the proposed solution inspect all traffic regardless of application, port or protocol?
Does the proposed solution inspect all traffic regardless of application, port or protocol?
 Does the proposed ZTNA Solution require any additional components to be installed in front of my private applications for content inspection?
Does the proposed ZTNA Solution require any additional components to be installed in front of my private applications for content inspection?
Versa Secure Access – A True Zero Trust Next Gen ZTNA Solution
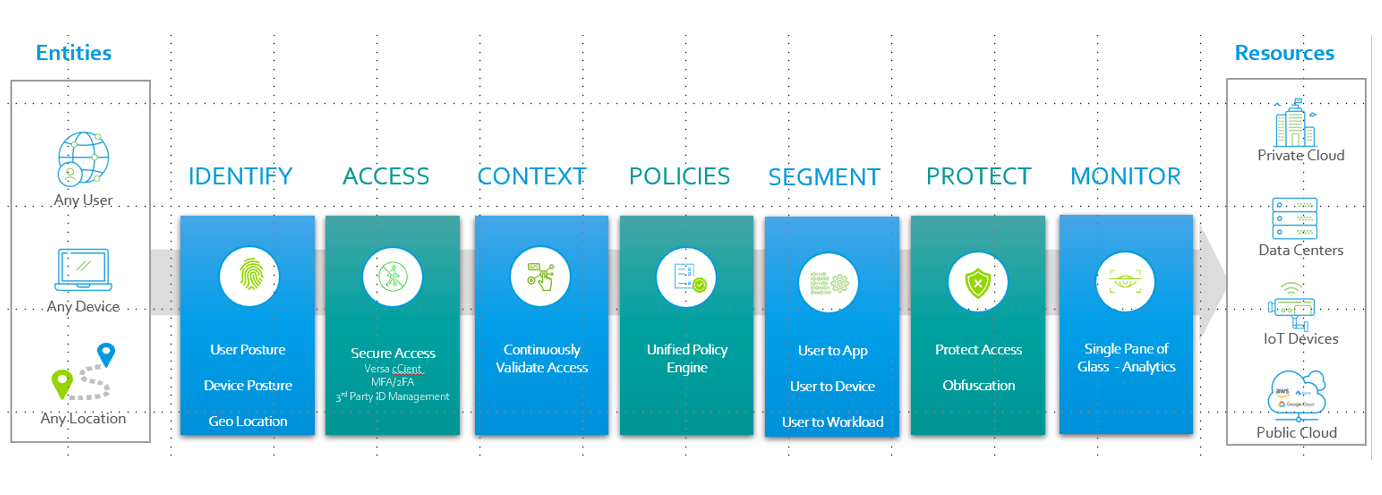
Versa Secure Access is a true Zero Trust ZTNA solution that enables customers to give secure remote access to their private applications for their remote workforce while ensuring that it confirms to all the 3 basic tenants of Zero Trust. Verify Explicitly – Identity, Context and Full L7 Content Inspection irrespective of port/protocol.
Verify Explicitly – Identity, Context and Full L7 Content Inspection irrespective of port/protocol.
 Use Principles of Least Privilege Access – Granular application control access policies.
Use Principles of Least Privilege Access – Granular application control access policies.
 Assume Breach – Full Content Inspection and continuous monitoring
Assume Breach – Full Content Inspection and continuous monitoring
Versa Secure Access is one of the core components of Versa Unified SASE and is delivered as a service from Versa Hosted Cloud Gateways.
Hit the Contact Us and drop us a line. We will get you in touch with a security expert to brief you how VERSA SECURE ACCESS can help you provide Secure Remote Access to your applications while adhering to the Zero Trust Model.

